Today I will continue to elaborate on the key features of Microsoft Sentinel - connectors, analytic rules and automation (SOAR). Enjoy! 🤗👇
If you haven't seen my previous post, I recommend you to see it before from here. 😄
But before I start, what do I need? Connectors!
Real-time data, unparalleled defense
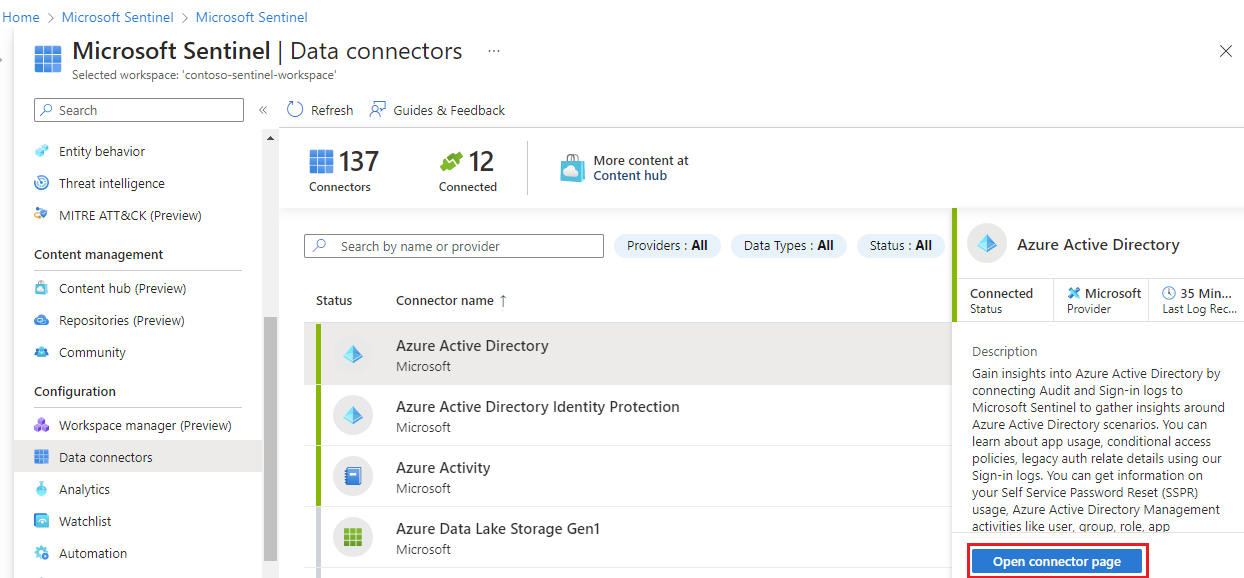
And before I start building? Materials (and knowledge 😋). The materials, in this case, are the data, without data there is no insight and without insight there is no response. So first we have to use the different Microsoft Sentinel connectors that will allow us to have the events of the assets of our infrastructure.
We can use connectors from different manufacturers. For example:
Microsoft: Office365, Entra ID, Azure Activity, Azure Firewall, Windows Server DNS, Defender for Cloud....
External: PaloAlto, Fortinet, Juniper, Checkpoint, Akamai, Google Cloud, AWS...
In this link you will find all the available ones.
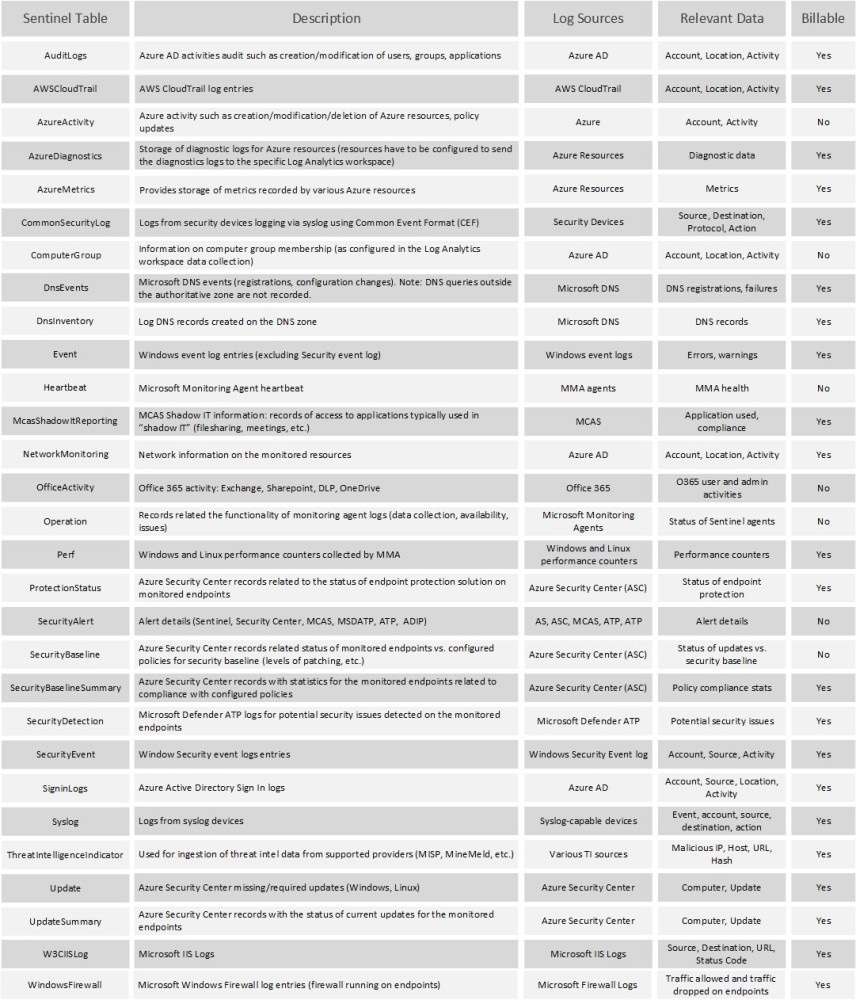
There are different tables associated with different events:
Once we have configured the connector (Microsoft's connectors are usually configured with 2 clicks), the ingestion starts, and, consequently, we will have the data to start... LET THE GAME BEGIN! 😄
I already have the data and now what? Analytical rules!
The different analytic rules allow you to search for specific events or sets of events in the infrastructure, and alert when certain thresholds or conditions are reached in the events to generate incidents, and then investigate them and respond to the threats with manual or automated processes (SOAR).
Types of analytic rules:
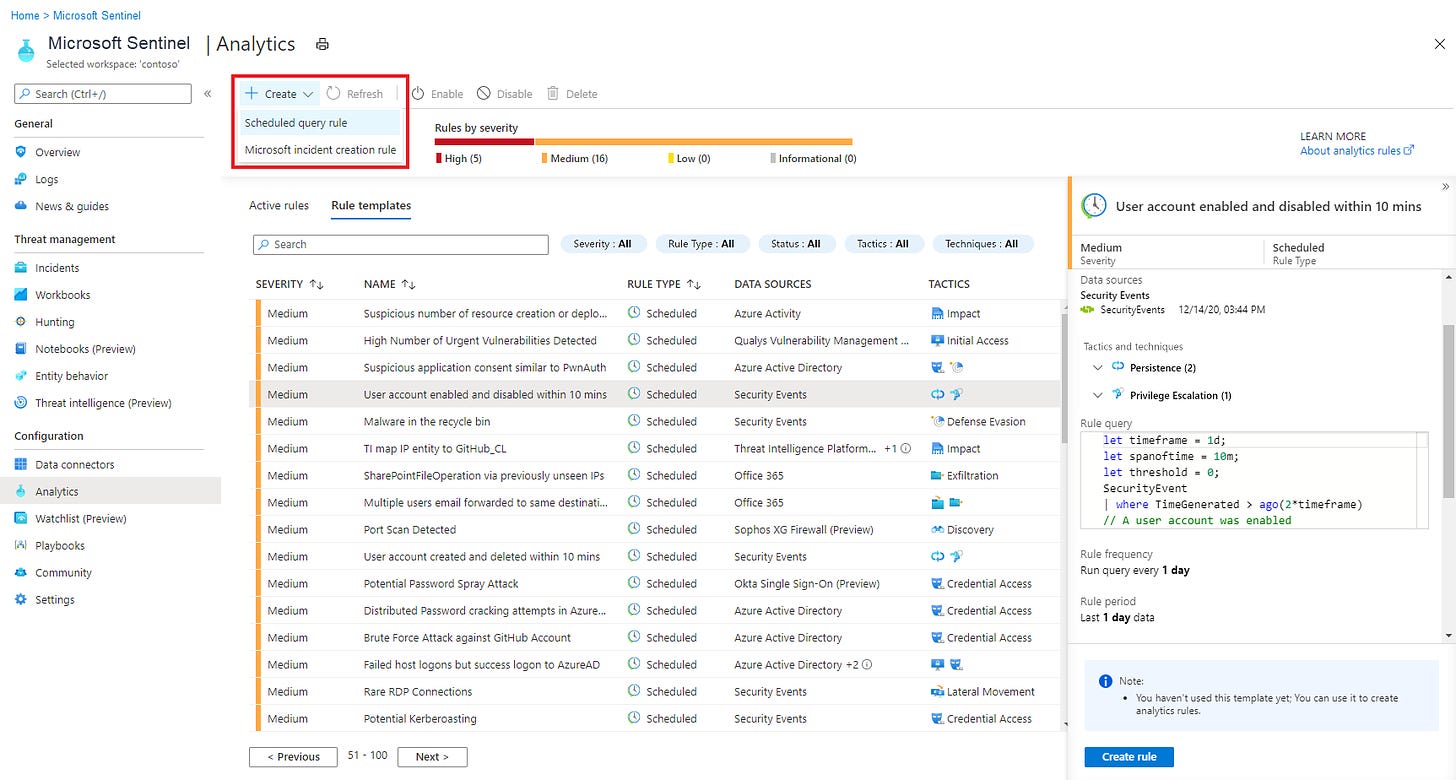
Rule templates: Set of pre-configured standard rules that you can activate once you enable the associated connector.
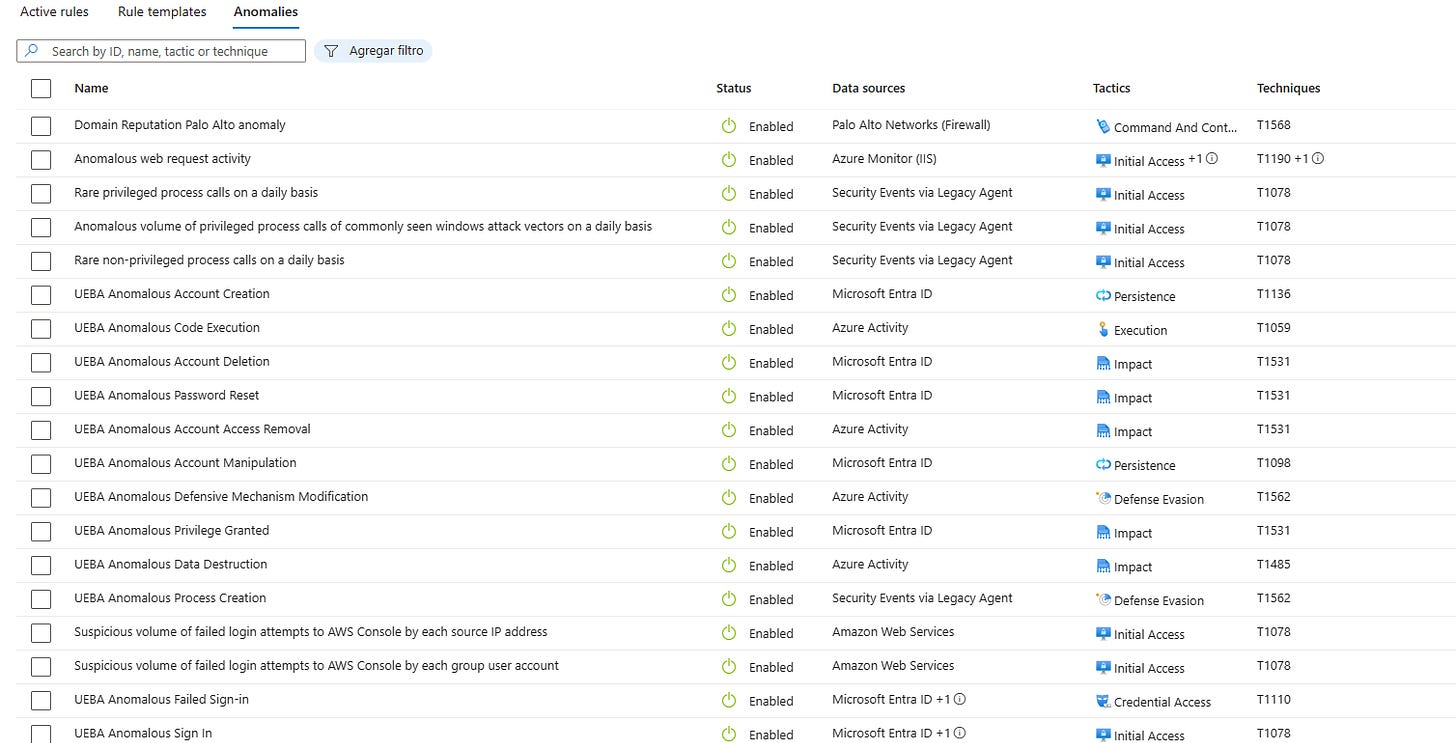
Anomaly Rules: Use machine learning to detect specific types of anomalous behavior based on your data. Each rule has its own unique parameters and thresholds, appropriate to the behavior being analyzed.
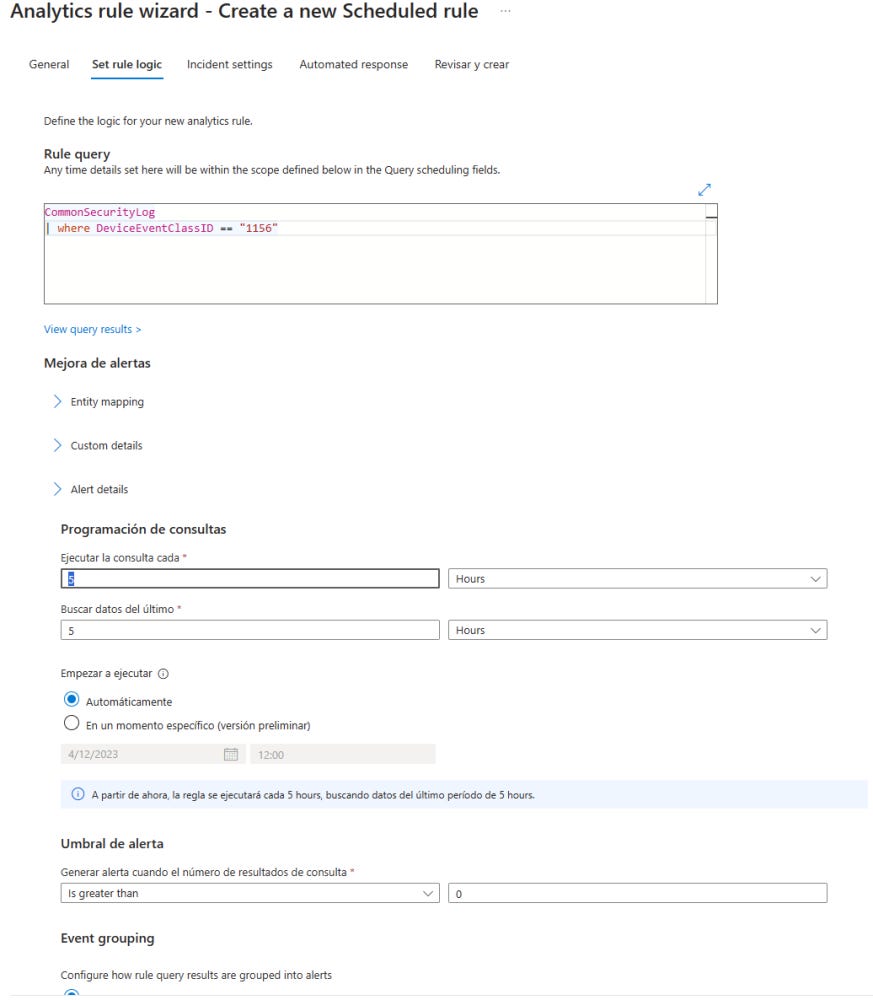
Custom rules: Based on your knowledge in KQL, you can generate custom rules based on your requirements and a time threshold. For example, if you want to create an incident when an Event X is generated in your Firewall (CommonSecurityLog).
NRT Rules: Allows to accelerate the periodic execution of the rule in the shortest possible time (<5 minutes).
What are the automated systems (SOAR)?
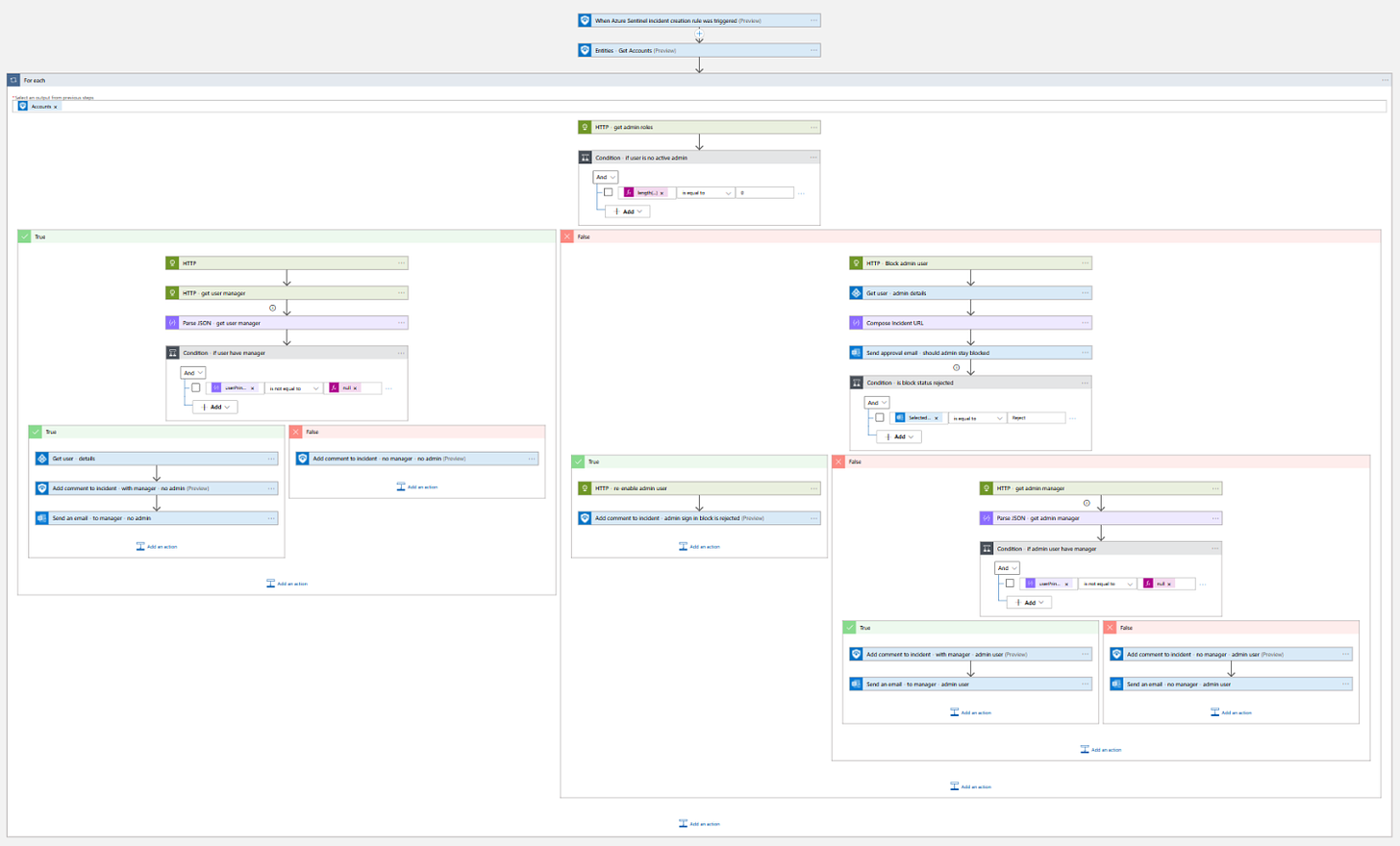
At Microsoft Sentinel we use what are known as Azure Playbooks to automate and orchestrate threat responses (SOAR).
These playbooks can be executed in two ways:
Manually, on demand: In response to a specific entity or alert.
Automatically: In response to specific alerts or incidents, triggered through an automation rule.
For example, if an account and a machine are at risk, with playbooks you can take measures such as isolating the machine from the network and blocking the account the instant the incident is generated.
Normally, this follows this pattern:
The trigger: The event that triggers the start of execution.
Information: Extraction of information (Account name, IP, file, device...).
The action: The execution to be performed (Lock account, isolate machine, send mail, create Teams...).
Here you will find a fairly extensive base of templates.
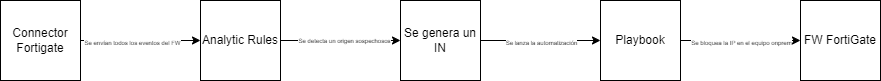
How are they used together? + Freaky Example
When a detection is generated with the analytical rule for a suspicious access to the server, an incident is automatically generated and the playbook is executed, which is responsible for blocking the IP in the external firewall equipment.
Here goes the geeky example 🤓, this time I'm going to base it on my childhood series, Dragon Ball. 🐉
One day, Piccolo, the Namekian, detects strange fluctuations in the System's data stream. The "Eye of Kami" analytical rule is activated, alerting him to possible intrusions in the system. Piccolo, recognizing the seriousness of the situation, decides to execute the "Makankosappo Firewall Attack" playbook. This maneuver automatically blocks any unauthorized access attempts, ensuring the stability of the network.
Meanwhile, Bulma, with the help of the SIEM Sentinel, identifies a pattern of suspicious behavior in the Z Warriors universe. The "Ki Frequency Detector" analytical rule highlights these anomalies. Goku, upon learning of this, decides to use the "Instant Transmission Security Scan" playbook to analyze it and upon corroborating that it is a true positive, launches another playbook "Threat Blocking Kamehameha", eliminating any malicious entities before they wreak havoc.
Finally, with the combination of analytical rules and playbooks, our Z heroes manage to keep the peace in Dragon Ball Cyberspace. 🌐🎖
(EXTRA, EXTRA!) AI, AI, AI, AI Who hasn't heard about AI/chatgpt this year?
If you want to go beyond the union of these features of Sentinel with generative AI, I recommend you to check the following video of my colleagues from Softeng where you can check all its potential.
Remember, collaboration and knowledge are the best weapons against digital threats. see you next week! 😎