Anatomy of a phishing AiTM attack 🎯
How does this type of attack work? How to protect yourself?
Hi, today I am going to explain step by step how attackers can bypass MFA in a sophisticated phishing attack.
Enjoy! 🤗👇
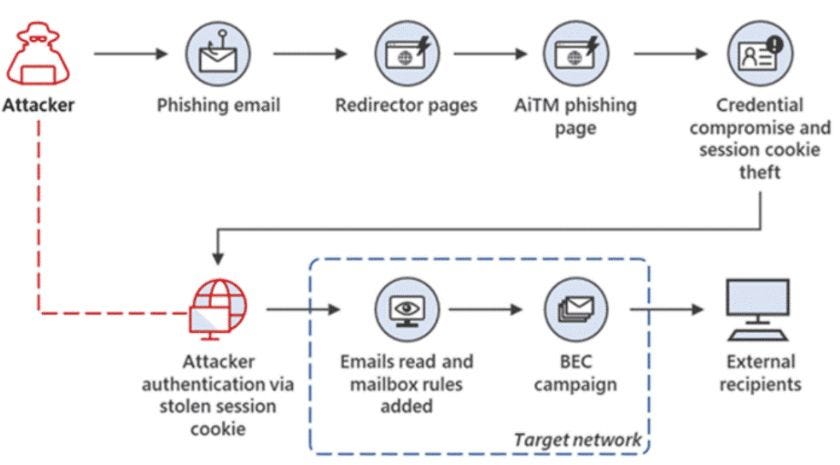
The user gets the typical phishing email, that your email protection won't have stopped it, yes, it doesn't stop it ALL 😂, that's why it is important that users are well aware and trained. 👨🎓
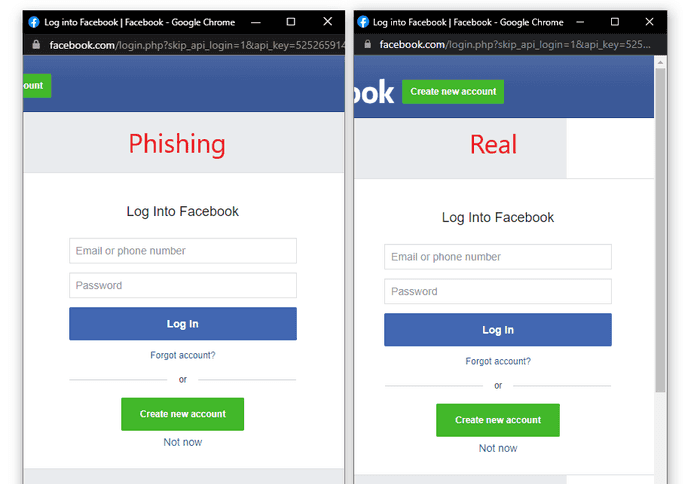
The unsuspecting 👤 user receives a link to a fake website, designed to look like the legitimate site, whereupon they log in and enter their username and password on this fake login page.
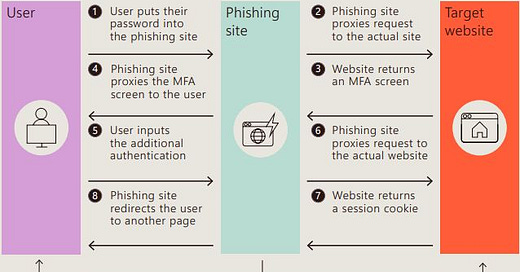
The phishing site acts as an intermediary (proxy) and sends the captured credentials to the real website.
This step is crucial, as it allows the attacker 👾 to follow the authentication flow as if he were the user himself.
Upon receiving valid credentials, the legitimate website requests additional authentication (MFA). This is usually a code sent to a mobile device, a push notification, or any other configured verification method.
The phishing site, acting as an intermediary, presents this MFA screen to the user. 👤 It looks normal to the user, as it is part of their login routine.
Confident that everything is legitimate, the user 👤 enters the MFA code or approves the authentication request on his secondary device.
The attacker 👾 receives this information and immediately forwards it to the real website, thus completing the authentication process on behalf of the user. 👤
Once authenticated, the legitimate website returns a session cookie, which the attacker 👾 captures.
This session cookie allows the attacker to gain access to the user's account 👤 without needing to re-authenticate.
Finally, to avoid arousing suspicion, the phishing site redirects the user 👤 to a harmless page or even to the legitimate website.
The user believes that there was a temporary problem and does not suspect that his account has been compromised.
👉 But... GameOver, your account has been COMPROMISED. ☠
🛡 TIPS to protect yourself from these types of attacks 👇
Implement conditional access policies: Limit access to your systems and sensitive data by configuring policies that take into account factors such as:
Corporate IP Addresses: Allow access only from known and approved IPs.
Device Status: Ensure that only secure and up-to-date devices can access.
Token Protection: Use physical or biometric tokens that are difficult to forge.
Educate users: Conduct regular training sessions so that users recognize phishing sites and understand the importance of not sharing their credentials.
Configure Security Alerts: Trigger notifications for suspicious access or login attempts from unrecognized locations.
Enable real-time threat detection: Use security solutions that analyze and respond to threats in real time.
With these measures, you should be more protected! See you next week! 😎